The other day a colleague of mine asked how I keep my web server secure, short of keeping up to date on patches and shit.
This is what I told em – you can fool a lot of people if you know what you’re doing with your server. Automated tools identify server software by the info returned by requests. Nmap is a prime example of a tool that attempts to identify services by analyzing the data returned by requesting and observing data returned by services running on ports. For example, if a service is running on port 22, and when you connect you are presented with the banner ‘Openssh’, more than likely, ssh is running on that port.
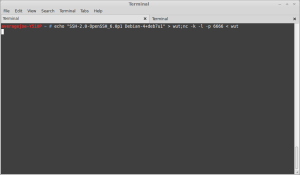
But what if I had netcat running on port 22 like so?
What if I was ACTUALLY running openSSH on port 53 because I don’t use a DNS server? If I show an old version of OpenSSH which will lure many scanners and skiddies to try all sorts of shit that doesn’t work. A pseudo honeypot.
Here are a few other ways.
+=============+
|.htaccess hax|
+=============+
The first thing I observe when I attack a web site is the server side language used. It helps me form an attack strategy and profile. So why not confuse the ever living crap out of your attackers by changing the extensions around? We can do this by modifying the .htaccess file with the “AddType” directive. For example, the following code will allow “asp” and “aspx” pages that execute as php:
AddType application/x-httpd-php .asp
AddType application/x-httpd-php .aspx
Then of course there’s JSP, ColdFusion, Perl, Ruby, and Python. Mix shit up.
AddType application/x-httpd-php .cfm
AddType application/x-httpd-php .cfml
AddType application/x-httpd-php .rb
AddType application/x-httpd-php .py
AddType application/x-httpd-php .pl
AddType application/x-httpd-php .jsp
Of course to further the rouse, setting the proper response headers will be essential. More on that later.
+======+
|Ports!|
+======+
We can use the same netcat trick I mentioned earlier with other ports common to microsoft such as port 139 (net bios) and 3389 (remote desktop).
For a listing of common ports, check this out.
+=======+
|Footers|
+=======+
If you put a “powered by X” footer on your web site, web spiders and auto scanners will pick up on this, as will your average skiddy. You’re not actually running phpnuke, but no one else has to know this right? You can throw off a lot of people using this, but don’t fool yourself, there’s always a dozen ways to identify CMS software. Example – you can verify someone’s WordPress version by checking the “readme.html” file in the WordPress install directory. And before you get any ideas, this won’t work on me, however the intent is to fool automated scanner and your average no talent wannabe.
+================+
|Response Headers|
+================+
HTTP response headers are the things the browser gets back when it sends a request. I don’t know why I said that, you SHOULD know this right? Anyways, response headers are usually blindly trusted by the client and include, but are not limited to: redirects, cookie info, sessions, response codes (like 404 file not found, 403 forbidden, 200 OK etc), cache, and server info. Assuming Apache there is a module which comes in handy for setting custom response headers – mod_headers. It comes with Apache by default, but isn’t always enabled.
You can set headers using mod_headers like so:
Header set X-Powered-By “ASP.NET”
Place this in your sites-enabled file or .htaccess file and the Microsoft specific “X-Powered-By” header will be sent to users who connect.
Mod headers will work for all other related headers except for ‘Server’ header. For this you need to use mod_security and the ‘SecServerSignature’ directive.
Edit the file /etc/apache2/conf.d/security and set the values “ServerTokens Full” and “SecServerSignature Microsoft-IIS/6.0” or whatever web server you wish to masquerade as.
That’s all for now. I plan on dropping source for my solo antivirus project soon as well as going public on a web server vulnerability I found last month.
Happy hacking!