Hello everybody!
Its been a wonderful new year. Full of new experiences and all that other stuff. Lately I’ve been running into a lot of .net stuff. Managed assemblies (compiled MSIL dlls) interacting with normal binaries as well as .net binaries. The beauty of it is most of the time, I can decompile them and look at the straight source code. It seems like less and less people are even bothering to obfuscate their code.
Today I’m going to cover MSIL decompilation, recompilation, editing, reversing, and the like. We’ll be going after Solar Winds’ license activation suite which is a collection of both .net managed assemblies and .net binaries. According to SolarWinds’ stock index, they’re worth over 44 million USD. You’d think with that kinda money they could afford to protect their software? Or not.
There are 3 ways to edit .net binaries and managed assemblies. The easy way, the hard way and the harder way.
The easy way – With Red Gate’s reflector and the reflexil plugin.
The hard way – Getting DILE to work – an open source effort at .net IL editing. The damn thing don’t work.
The hardest way – With ildasm and ilasm – microsoft’s IL disassembler and assembler programs.
I’ll go over each.
The first tool, Red Gate’s Reflector is a payed tool, but totally worth it. A hundred bucks a license, its one of the few pieces of software I’m willing to pay for merely for convenience.
The 2 best plugins are Reflexil (http://reflexil.net/), used for editing the IL code and Deblector (http://deblector.codeplex.com/) which is an excellent .net debugger.
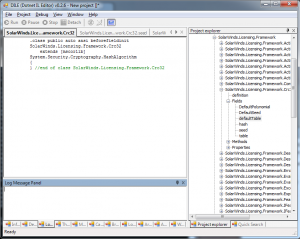
Tool number 2 is DILE (http://sourceforge.net/projects/dile/) which stands for Dotnet.I.L.Editor, clever ehh?
I’m all for open source, however not when nothing works. Maybe its because I’m using the 64 bit version? Dile also supports a debugger, though once again, I never got it working.
Lastly the hardest method of the 3, is more than 1 tool. ilasm for assembling, ildisasm disassembling, and MDbg for debugging of .net assemblies. http://msdn.microsoft.com/en-us/library/ms229861.aspx ilasm and mdbg are both CLI tools, but ildisasm isn’t. All 3 come with visual studio. I say its the hardest because of what’s involved.
===On with the show===
Today we’re attacking Dameware’s Remote support, a suite of tools that allows remote administration of windows systems. I was checking this tool out the other day for its remote task manager capabilities and ease of use.
The binary is nothing special. In fact, the app isnt even made in .net at all. its a C++ application. The licensing application on the other hand is. 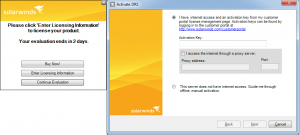
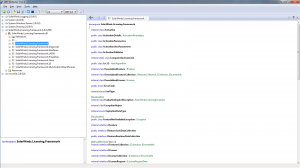
Loading up the licensing application with our .net decompiler, we see the application is just a stand alone app that feeds from external managed assemblies. 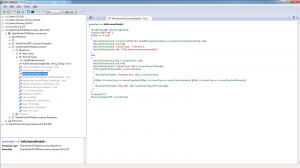
The managed assembly in question is the SolarWinds.Licensing.Framework.dll. Loading that up, we see many methods, classes and function calls.
I’ve saved you from some digging and isolated the internal class ‘LicenseValidator’ and its method ‘IsLicenseValid’.
As you can see, the function is what we’re looking for. We see what types the method takes:
byte[] licenseData, byte[] signature, byte[] nodeLockInfo, byte[] serialNumber, LicenseType type, byte licenseInterfaceRevision
We see the return value – true or false.
We know what we need to patch to make every license we pass valid.
Now, how do we do it?
===The easy way===
The easiest way is with Red Gate’s .net reflector and its sister plugin reflexil.
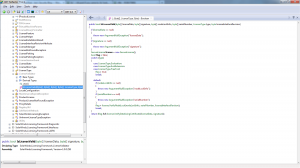
Here, we load up the plugin and see the MSIL instructions in the bottom window.
We right click and choose ‘replace all with code’. The mini .net compiler window pops up.
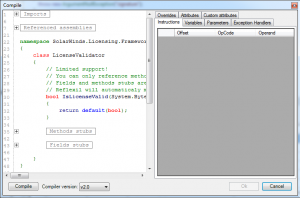
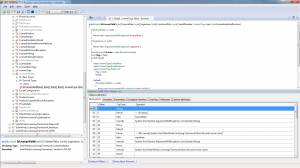
Next we re-code the function to our liking. In this case, I am making the code always return true. We then hit the ‘compile’ button and our instructions window on the top right shows our new MSIL instructions.
———
ldci4.1
ret
———
ldc.i4.X—loads a 32-bit constant (X from 0 to 8) onto the stack
ret – return.
This makes sense right? Load the value ‘4’ onto the stack and return. Unlike traditional assembly where one would assume to ‘push 1’ for the value of true, we are pushing 4. Why? I don’t know, .net is weird like that 😀
After pressing ‘ok’, the new instructions we compiled will be present in the lower right pane. All that’s left now is to save our changes.
This is done by right clicking the assembly on the left, choosing the reflexil plugin, then choosing ‘save as’ which brings up a save window.

And that’s it. Easy as pie.
When we re-disassemble our managed assembly, the function now shows the code we patched seen here with ilspy: 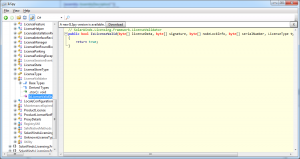
===The hard way===
Sometimes you may night have the hundred bucks to shell out on Red Gate’s Reflector. You’re a hobbyist with not too much cash, but an interest to learn. There is hope though, provided you’re willing to re-code some stuff. DILE off of source forge offers a similiar experience for free. Problem is, the THING DONT WORK. At ALL. Maybe its because I’m running 64 bit windows and the version I have is inferior? Or maybe the project was abandoned in 2011. Either way, its fail.
I want to believe it works, but signs point to doubt on this one.
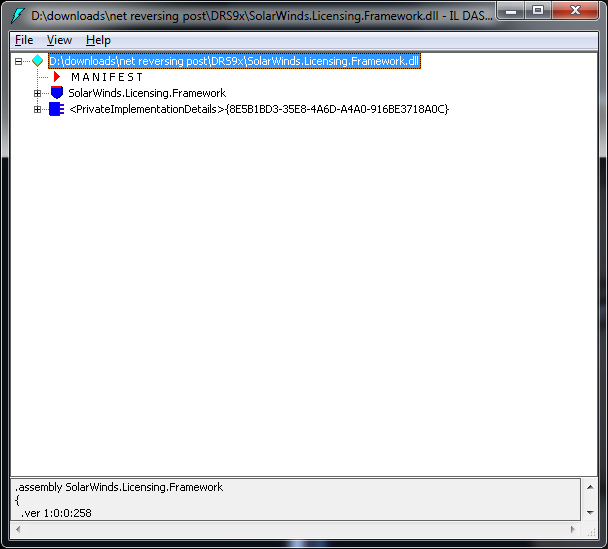
===The harder way===
There is nothing wrong with this method. It does work. There are more steps, but at least its free. The tools come included with Visual Studio Express.
A brief run down: First we disassemble the binary / assembly to a .il file, then edit the code, save the file, then re-compile with ilasm, assuming you got the MSIL syntax correct (which isnt exactly easy to find reference wise). If you team this with something like ilspy, it will save a bunch of work of tracking down the method / class names.
We use the ildisassembler tool for this:
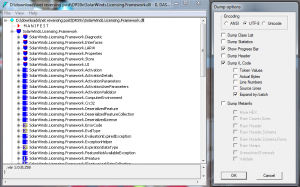
Click file, then dump, then select a directory to place the disassebmled code in.
Now we open the .il file (msil code) in notepad and look for the function we want.
We already know we’re searching for the class LicenseValidator, and its method IsLicenseValid.

All we have to do now is replace the MSIL code with our other code that makes the code return true.
.method public hidebysig newslot virtual final
instance bool IsLicenseValid(uint8[] licenseData, uint8[] signature, uint8[] nodeLockInfo, uint8[] serialNumber, valuetype SolarWinds.Licensing.Framework.LicenseType ‘type’, uint8 licenseInterfaceRevision) cil managed
{
// Code size 2 (0x2)
.maxstack 8
IL_0000: ldc.i4.1
IL_0001: ret
} // end of method LicenseValidator::IsLicenseValid
Look familiar? ldc.i4.1, then ret? Yeah, same as our reflexil code. If you need to reference other code, I suggest reading up on MSIL syntax. Another convenient method is to code something up in visual studio, then decompile it with the ildisasm tool and copy + paste. It works.
Now we need only re-assemble our code.
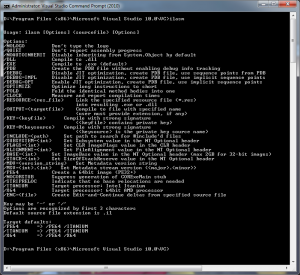
Run the ilasm command against the saved .il file (you saved it right?) along with the proper command line arguments such as /dll for managed assemblies.
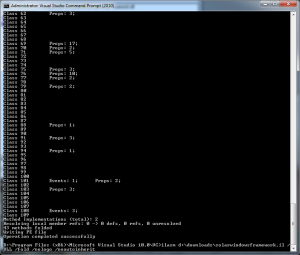
Assuming all goes well and you didn’t make any syntax errors, you’re all done. The managed assembly or exe will be assembled in the same directory as the .il file.
One thing worth noting is you need all the resource files and crap that ildisasm drops into the same directory as the .IL file, otherwise the thing wont complile:
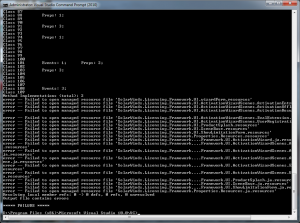
And that’s all there is too it. We place the modified managed assembly in the same directory as the licensing application and presto! The application accepts any license we pass it.
More work is involved if the code is obfuscated, but that sounds like another post for another day.
The next post we’ll be attacking a popular windows mail server. Another .net application from a company who doesn’t feel like fully obfuscating their binaries.
Happy cracking!
