People often wonder “Joe, how the heck do you know if an AV is worth its weight in sand?” and to them I answer “I have to test it first”.
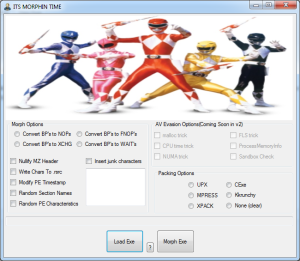
This is one of my tools I coded up. Presently I have to do AV evasions with a debugger, modifying the entry point and looking for a ‘code cave’ to place the fine tuned opcodes. It’s not exactly automated – YET. The other settings though work just fine. The concept is this – take a known sample, mess with it, then send it back to the AV to see if its found out.
Since I had “morphing” on the mind, I chose the “Mighty Morphing Power Rangers” as a theme.
If you want to know more about modifying a PE file and its respective structure, then the source (made in C#) will help.
Because I’m a nice guy, I’m going to share the exe as well as include the source code. Be on the look out for v2 when I get around to adding AV evasion modifications statically rather than with source code or with a debugger.
It comes with the packers listed (CLI versions) – mpress, UPX, xpack, cexe, and kkrunchy.